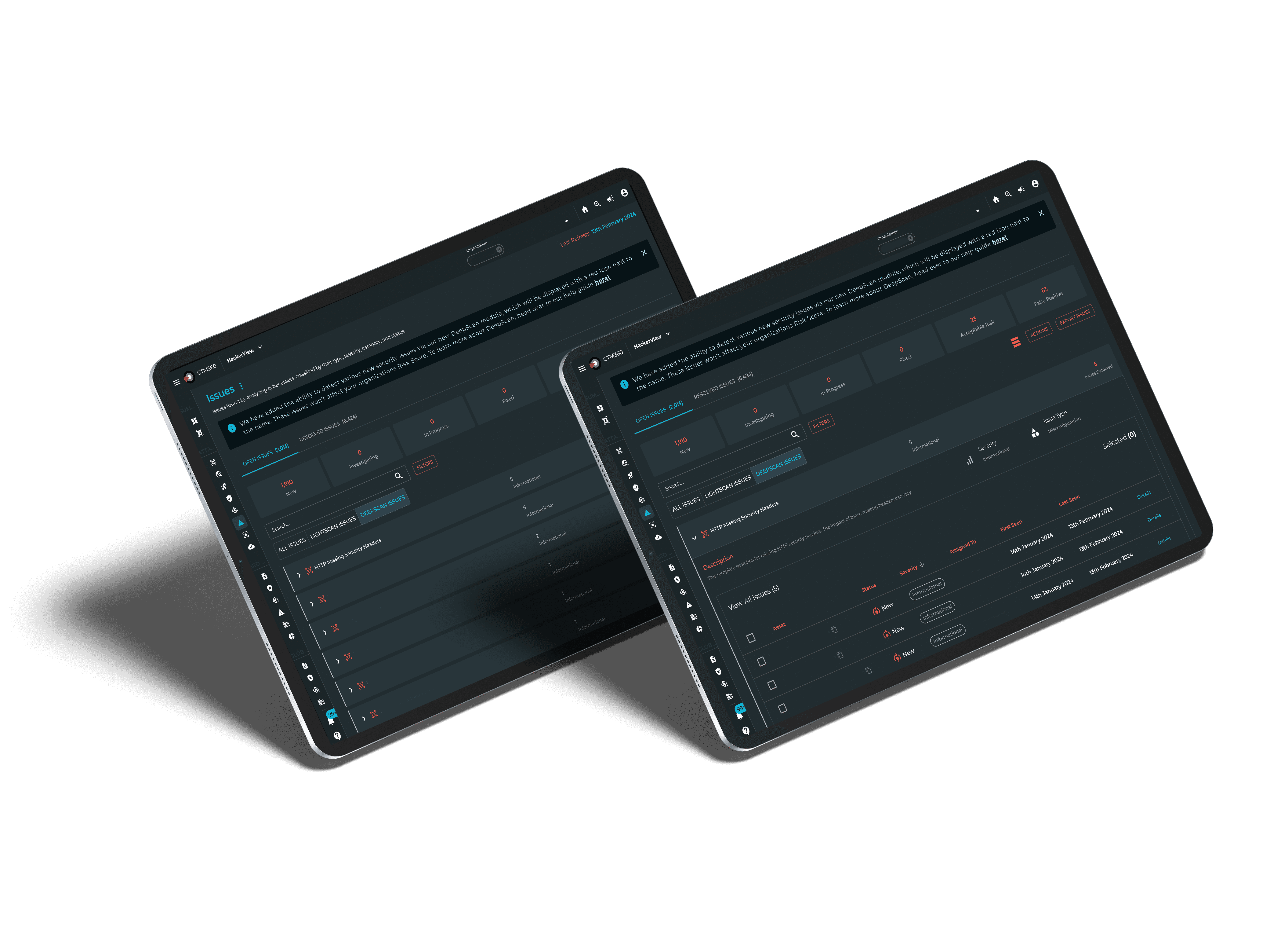
Centrally monitor cyber risk across your supply chain
Gain instant insight into the security posture of your vendors, partners, and 3rd parties.
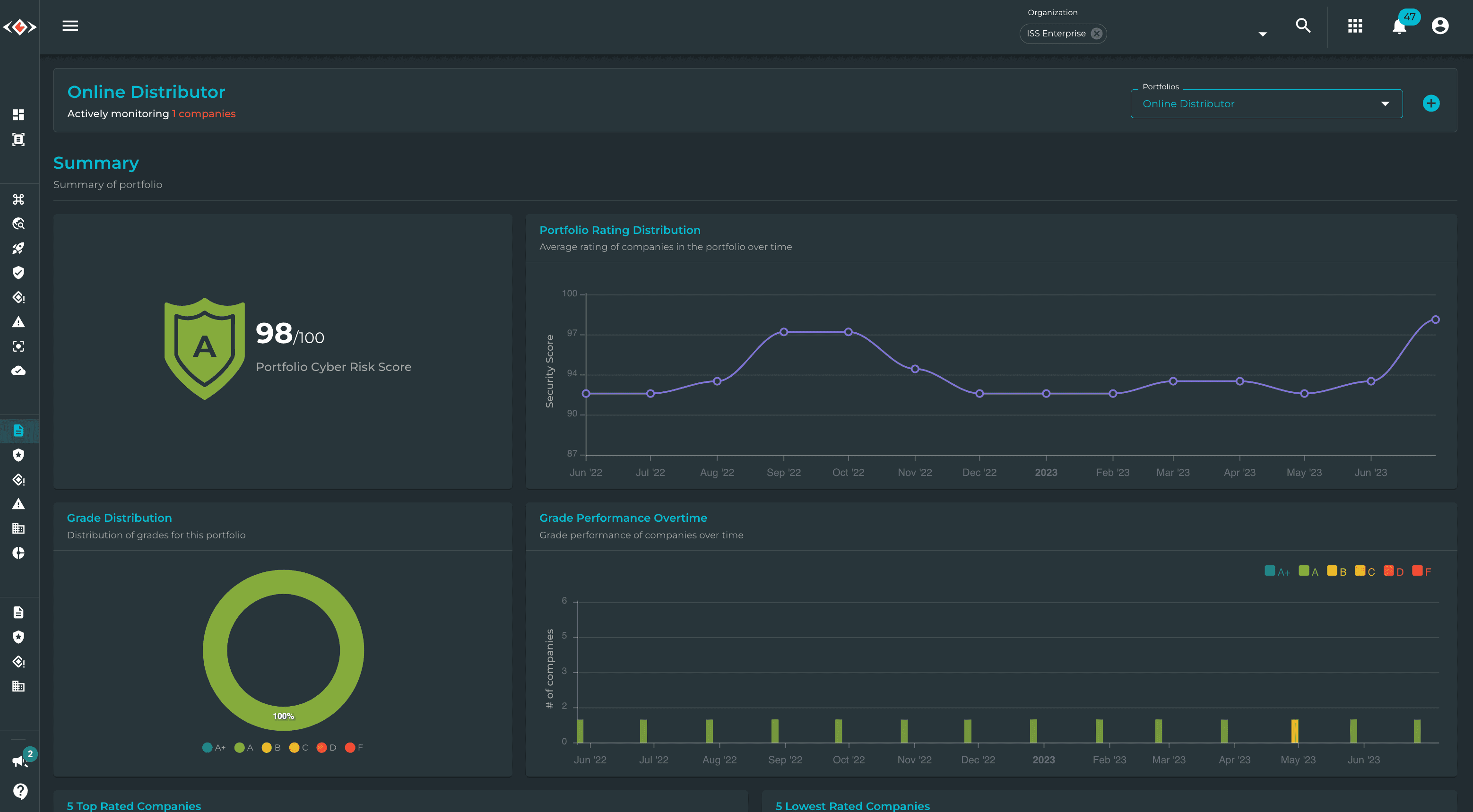
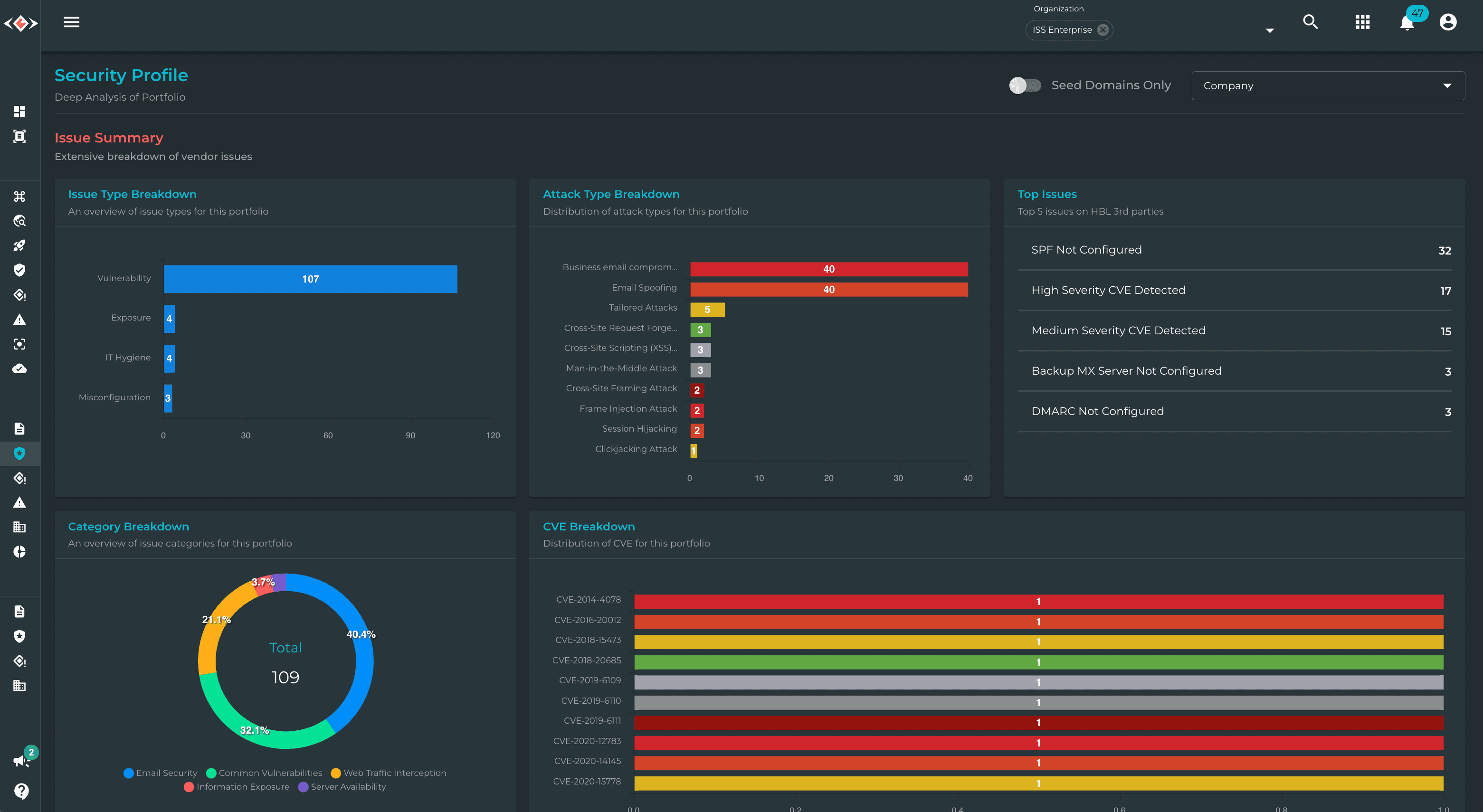
Aggregated security analytics
Conduct due diligence by viewing the most common issues and areas of concern associated with your 3rd-parties.
Manage your portfolios
Effectively manage all monitored companies in one or multiple portfolios with the ability to segment and prioritize at an individual company level.
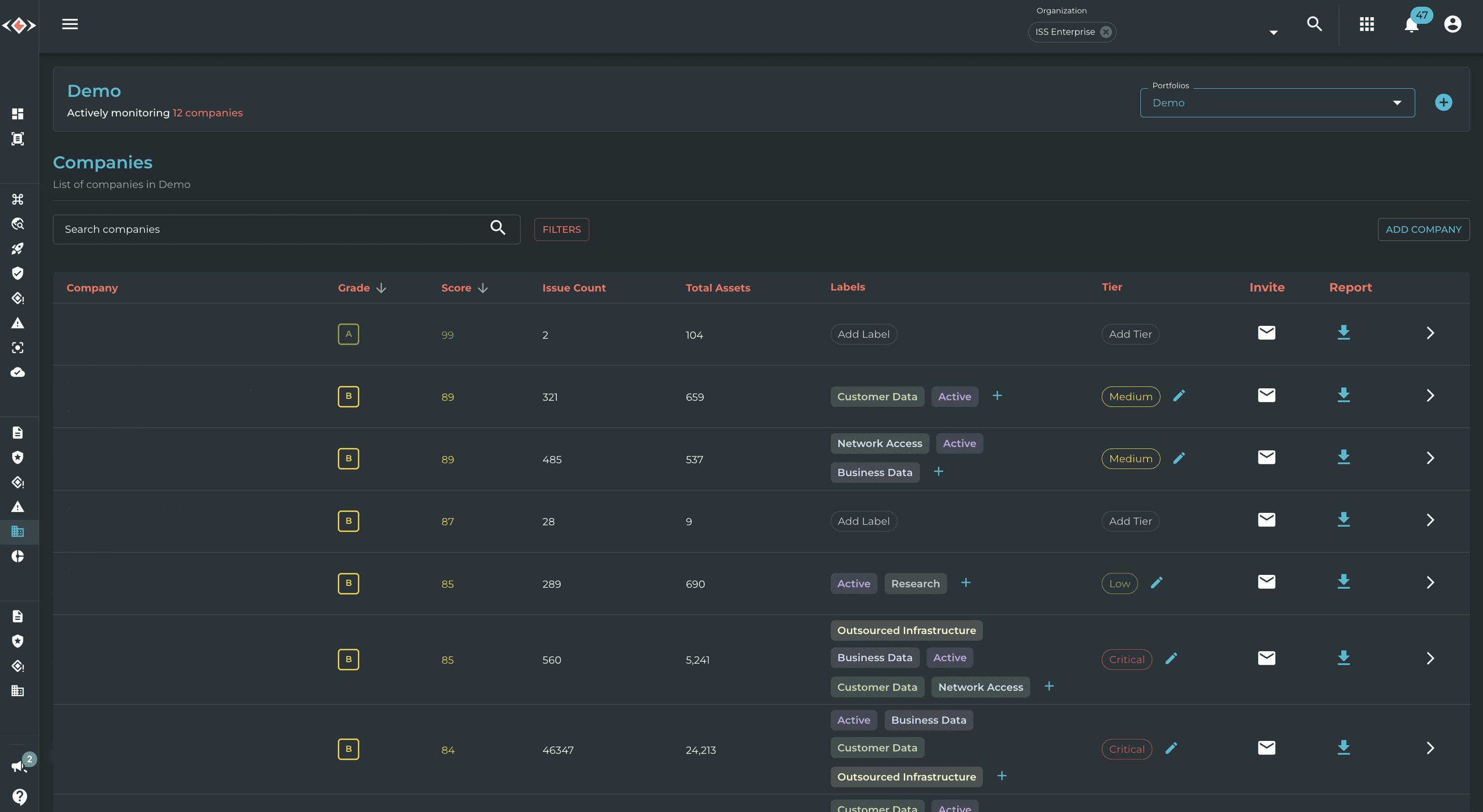
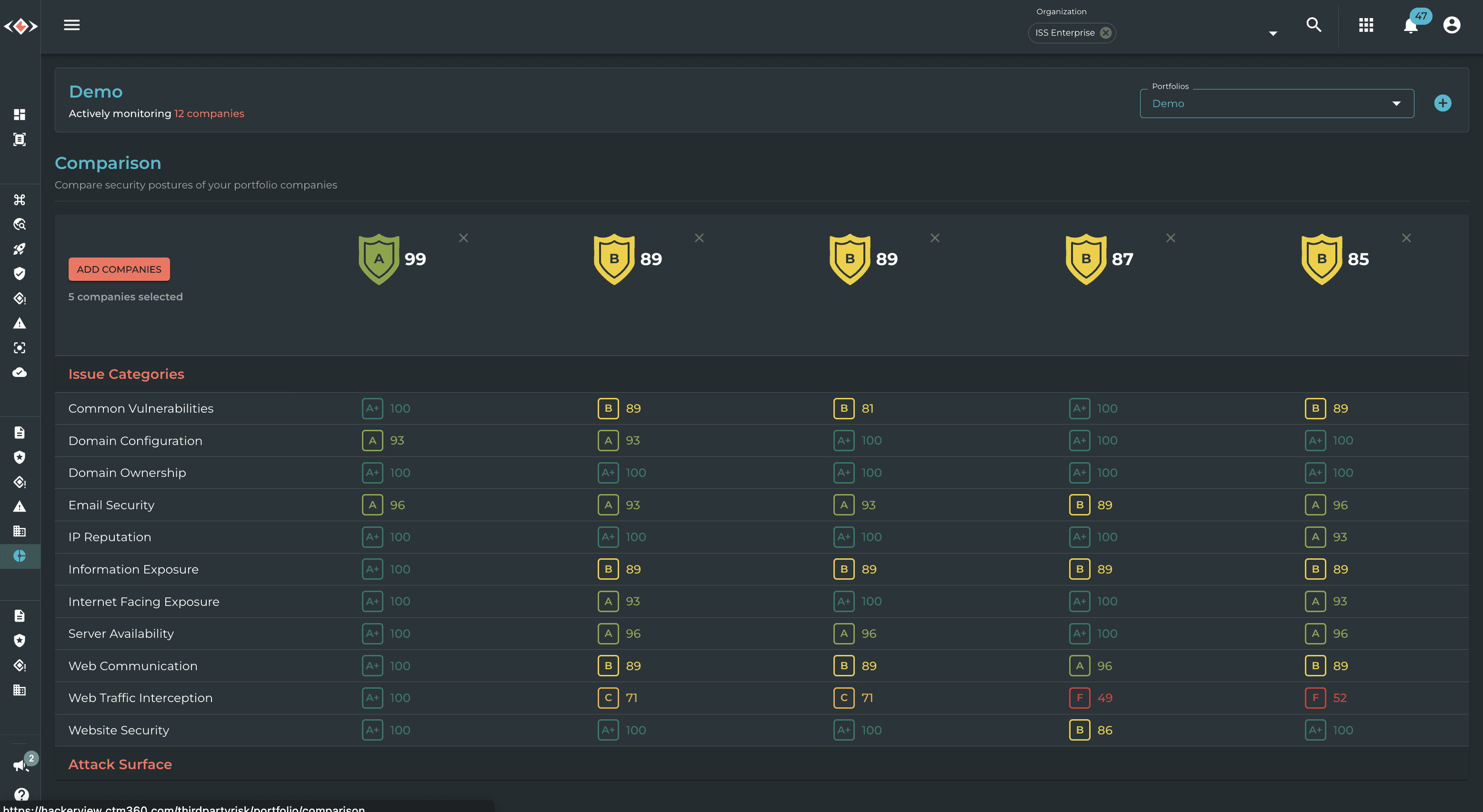
Security Posture Comparison
Efficiently compare the security posture of your monitored companies.
Solutions by

Frequently Asked Questions
What is the Third-Party Risk Management Module (TPRM)?
Third-Party Risk Management, or Supply Chain Risk Management, is the act of monitoring your vendors, suppliers, partners, and even potential prospects to gain insight into their Cyber Risk Posture and their External Attack Surface.
What differentiates Third-Party Risk Management from Global Benchmarks?
Entities within Global Benchmark are assigned to portfolios based on their operating country and industry sector. On the other hand, entities within Third-Party Risk Management are added based on your requests. Moreover, the two modules differ in the level of information they provide.
What kind of information will be visible to me here?
Similar to the Global Benchmarking Module, you can see a high-level overview of the portfolio's Security Profile. Over here, you can view the classification and breakdown of the various issues within the organizations in this portfolio. You will also gain insight into the various technologies and environments used here. Moreover, you will be able to dig deeper into specific entities present within these portfolios and view the applicable issues without knowing the assets they impact.