CTM360 has recently observed a spike in the compromise of genuine social media accounts impacting organizations and individuals. The compromise sees the original account holder losing control of their account, and then followers targeted in each successive breach..
09 Oct 2023

These attacks are not seen to be isolated incidents and are part of a campaign that operates based on a network ripple effect. The threat actor targets each compromised account’s followers through social engineering, offering bitcoin or financial investment opportunities. Victims typically treat these posts as genuine as messages originate from within the account holder’s trusted network. Scammers take over your social media account to:
● Pretend to be you and trick the people who follow you.
● Share posts on the account saying they made a lot of money by investing a certain amount.
● Convince the account's followers to share their personal information.
● Lure them with high monetary returns and make them join fake trading platforms that require initial investment.
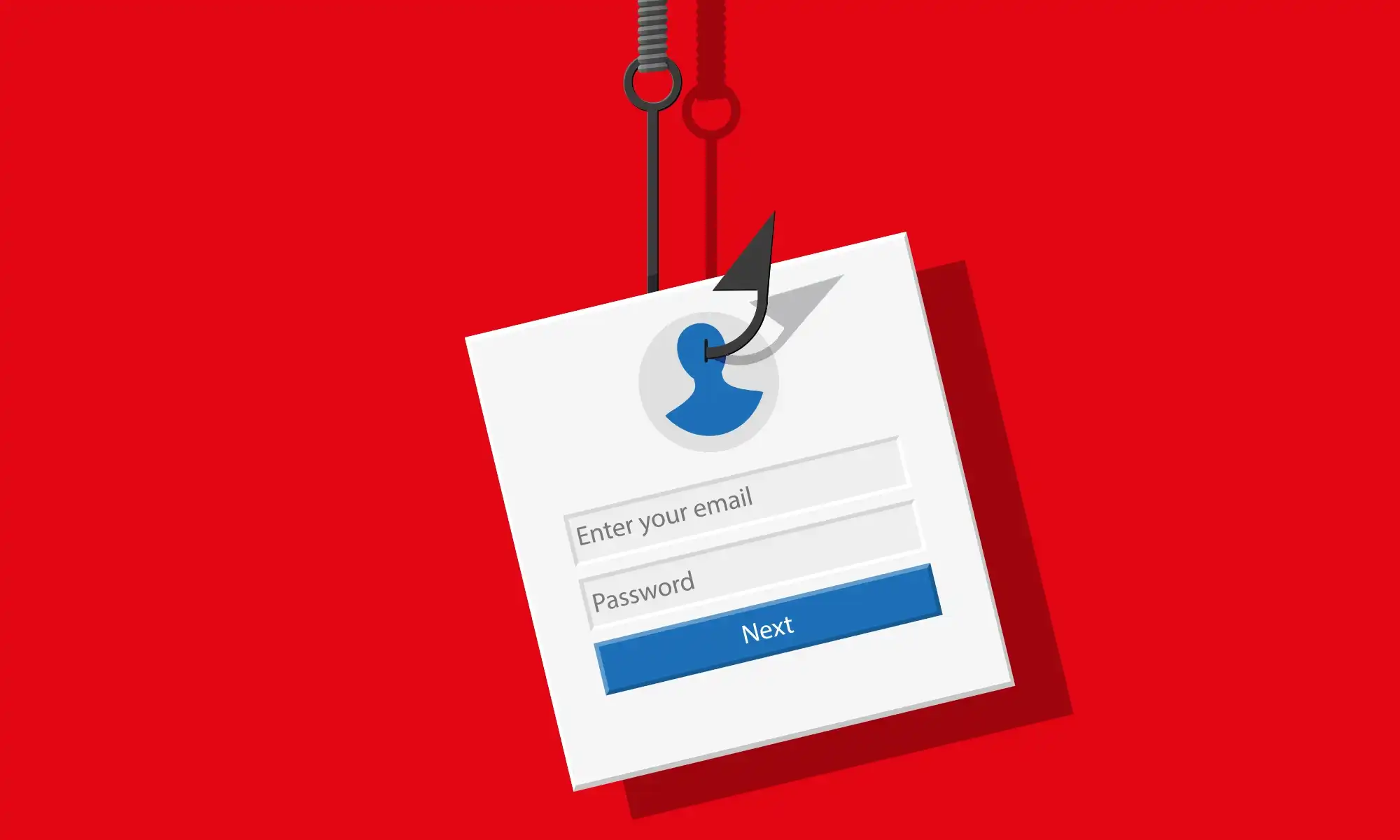
● Trick the victims into giving away SMS OTP codes sent to their phones, eventually letting the scammers hack the accounts.
● Upon gaining control, the scammer changes all details, including passwords, mobile numbers, and corresponding details.
Commonly known as Social Media Account Takeover Fraud, the evolution of this attack is that it continues to move from account to account, allowing the scammer a window of opportunity to target all followers. This advisory is designed to give you important advice and details on keeping your social media accounts safe and preventing your online connections from becoming targets of these scams. Account takeover fraud isn't restricted to just social media platforms; it can also apply to email accounts, online banking accounts, online shopping accounts, and more. Whilst CTM360 has historically facilitated the process of recovering compromised Instagram accounts for victims with considerable success, there have been policy changes wherein the platforms are increasingly entertaining only direct requests from the original account holder. Recovery for such accounts is challenging for the end-user due to changes in the policies of the social media platforms impacted, notably Instagram and Facebook.
How do scammers take over your social media accounts?
1. Phishing attacks: Through deceptive emails, texts, or calls, they impersonate reputable companies to trick you into divulging sensitive information or visiting phishing sites.
2. Malware Infostealers: Hackers infect your device with software that records your input and sends it to them.
3. Credential stuffing: Scammers use software bots for brute-force attacks on passwords, often evading website security measures.
Recommendations:
- Enabling Two-Factor Authentication (2FA) on all your social media accounts is the best way to minimize risk. Ensure the second factor is linked to your active mobile number, or use an authenticator app with securely stored backup codes.
- For organizations that engage third parties, such as marketing agencies and PR firms, there is elevated risk, and it is recommended to ensure the following: a. Ensure 2FA is a mandatory requirement and emphasize the criticality across all engaged subcontractors. b. Actively audit access of all third-party contractors and ensure a need-basis level of minimum access. Granting administrator privileges is actively discouraged and should reside with an internal stakeholder. c. Do not allow personal accounts of the employees of third parties to be used for handling your organization’s account.
- Exercise caution when it comes to clicking on links shared in messages, even if they appear to be from trusted friends. Be vigilant about potential phishing attempts.
- If 2FA is enabled, do not share One-Time Password (OTP) codes with anyone, including friends and family, unless you are certain it's for a legitimate and known purpose.
- Understand the risks associated with oversharing personal information online. Be mindful of the data you disclose, as malicious actors can exploit it. Protect your privacy by sharing only what's necessary.