Content
Phishing attacks via QR codes are on the rise!
13 Jul 2023

CTM360 has observed a recent scam tactic involving phishing emails that use QR codes. This scam represents a prevalent phishing variant where individuals scanning the QR code are directed to a fake login page that closely mimics a legitimate email service.
What is QR Code Phishing?
QR code phishing involves the malicious use of Quick Response (QR) codes to redirect unsuspecting users to fraudulent websites, capture sensitive information, or install malware on their devices. QR codes, which are commonly used for convenient access to various digital content, can be manipulated by cybercriminals to mislead and exploit victims.
Types of QR Code Phishing:
- Malicious QR Codes: Attackers can generate and place their QR codes in public spaces or on fake promotional materials. These QR codes may lead to fake websites that mimic legitimate ones, designed to steal your personal information.
- Overlay Attacks: Cybercriminals can create a malicious overlay on top of a legitimate QR code, leading users to a fraudulent website or application. This overlay can be placed on physical objects like posters or product packaging.
- Fake App Downloads: Attackers may encourage users to scan a QR code to download a malicious application that mimics a legitimate service. These fake apps can compromise your device and steal sensitive data.
Why do Threat Actors Use QR Code Phishing?
QR codes are particularly effective in these attacks as they can evade standard email security measures, including URL scanners, making it difficult to detect any signs of a suspicious link or attachment in the messages the QR code is pasted in. This allows attackers to bypass email protections and trick unsuspecting victims into providing their login credentials or other sensitive information.
Example of the Attack:
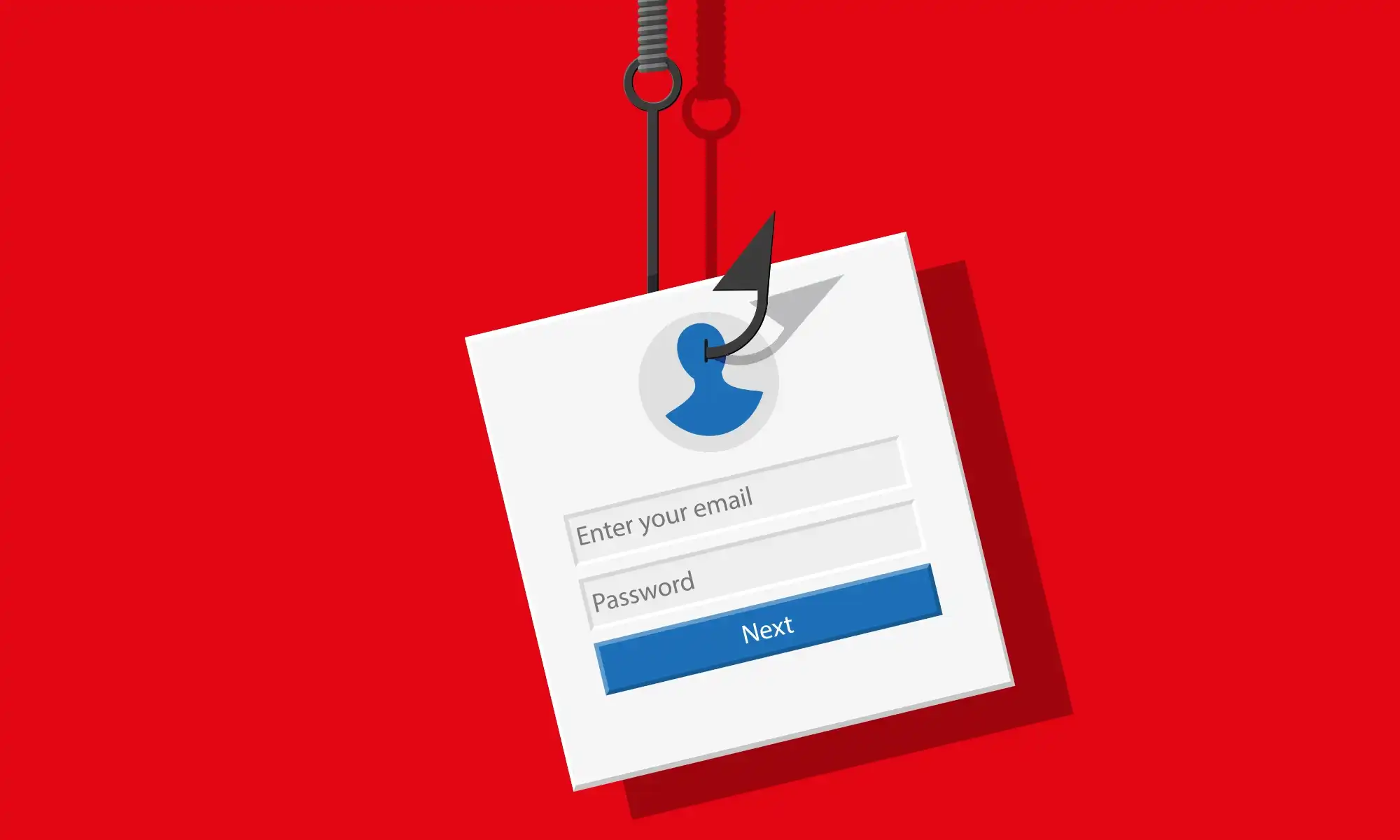
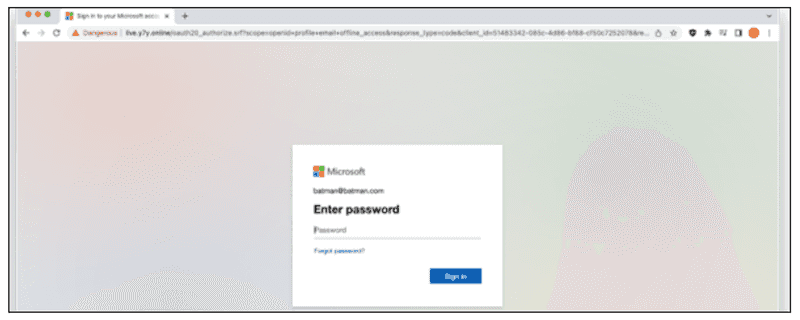
The attacker generates a legitimate QR code by claiming that your email password has expired. They distribute the QR code through different channels, including email, social media, or even physical flyers.
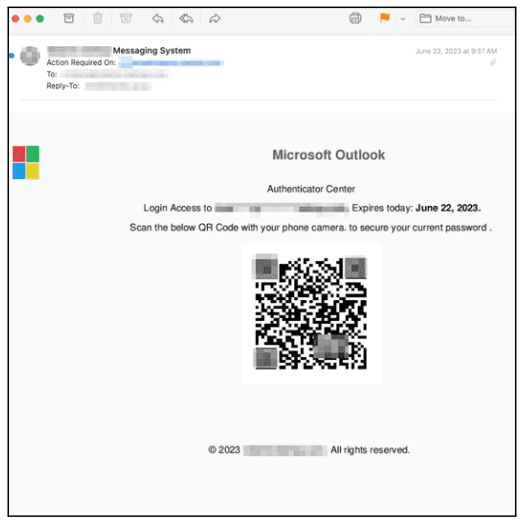
When the victim scans the code using their smartphone or other devices, it redirects them to a malicious website that resembles a genuine site. The website prompts the victim to enter their login credentials, which the attacker can then steal and use for malicious purposes.
Recommendations:
- Always verify the source and authenticity of QR codes before scanning them. Use official company websites or trusted sources to obtain QR codes. Be cautious when scanning codes from unknown or unsolicited sources.
- Raise awareness among employees and individuals about QR code phishing risks. Conduct regular training sessions to educate them on safe QR code practices, including verifying the source and checking URLs.
- Before scanning a QR code, take a moment to inspect the associated URL or website address. Look for unusual or suspicious elements such as misspellings, extra characters, or unfamiliar domains.
- Be extremely cautious when a QR code takes you to a website that asks for your personal information, login credentials, or payment.
- Make sure to enable two-factor authentication to enhance the security of your accounts and protect them from unauthorized access.